Removing Browser redirect hijacks (solved!)
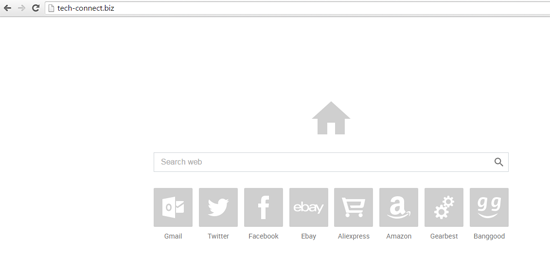
You will know it if you have a browser redirect virus, also known as the google redirect virus or malware. The various iterations of the dreaded browser hijack or redirect removal solution is a mystery to many on internet forums. It’s nasty and resists every attempt at removal. It is invisble, undetectable by all the malware scanners and antivirus programs including Norton’s Powerful Eraser tool, bitdefender speciality tools, eset’s usually very efficient scanner in ramdisk, in fact just about everything.
We had a business client with this infection and after struggling to remove it, we decided to persevere until we found the mechanism and methods to remove it. Unfortunately, it seems each variant or type of this infection has it own methods to provide a successful removal. There is no single access point to remove it.
But good news! We offer an online (remote access) service to remove this, along with all the other bugs on your computer. If you are anywhere in Australia call or email to arrange a good time for us to log in for you.
www.wiredoffice.com.au has been providing trusted service for over 15 years and is a Microsoft registered partner, and a Microsoft Certified Professional (MCP).